Agent Governance
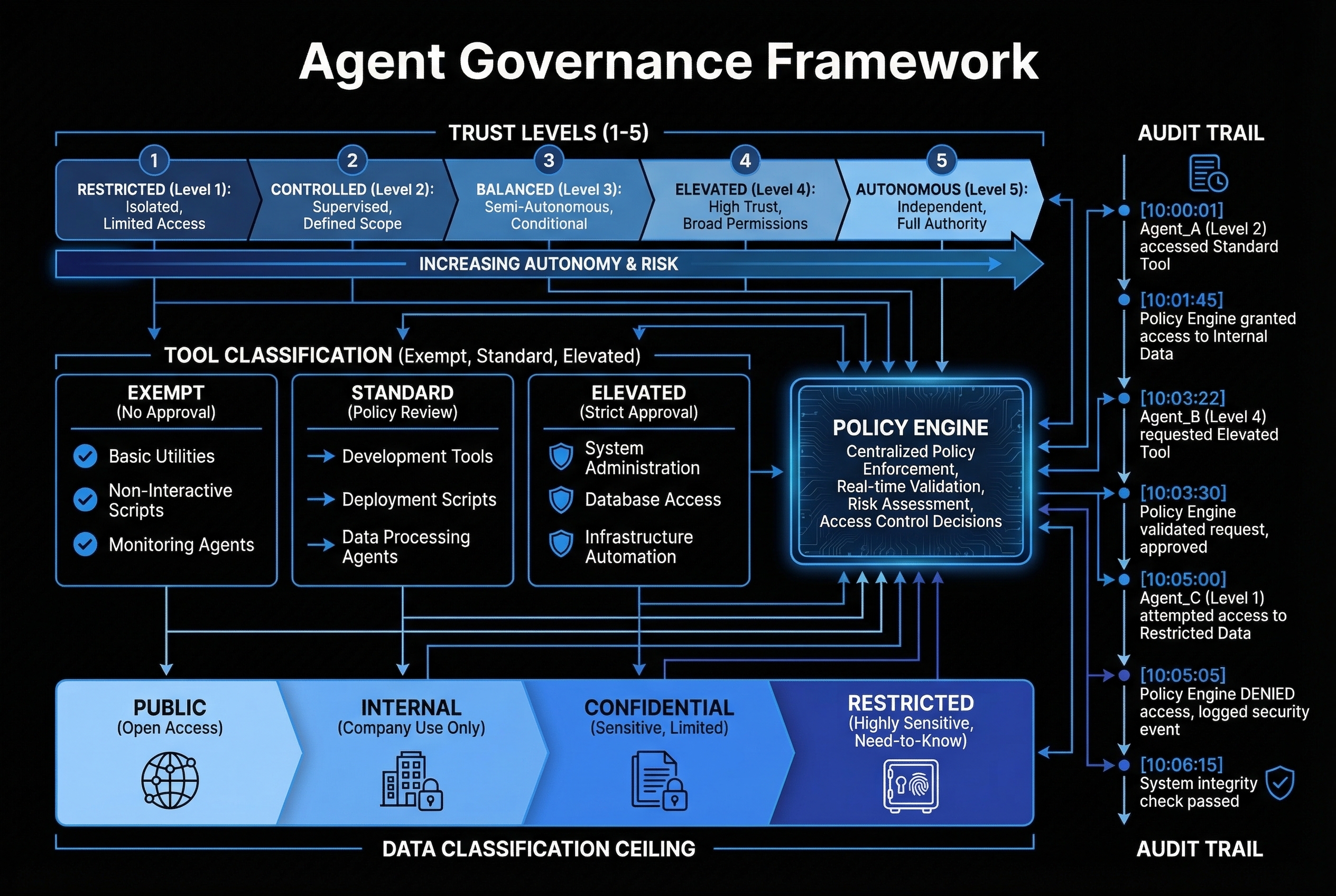
Built on Gartner's AI TRiSM framework. Five trust levels, four data classification ceilings, three tool risk tiers, and an append-only audit trail — all enforced with under 200ms overhead for standard operations.
Trust Levels
Graduated permissions from read-only observation to full autonomous operation.
How It Works
Policy enforcement at every decision point in the agent lifecycle.
Agent Spawns
Agent manifest loaded with declared trust level and capabilities
Manifest Loaded
Policy engine validates manifest against conductor tier matrix
Trust Assigned
Trust level determines tool access, data ceiling, and delegation rights
Action Evaluated
Every tool call checked against trust level, data ceiling, and risk tier
Audit Logged
Append-only SQLite WAL records decision, context, and outcome
Key Capabilities
Enterprise-grade controls that stay out of the developer's way.
Trust Levels 1–5
Five graduated permission levels from read-only observer to fully autonomous agent. Trust is assigned at spawn, inherited by sub-agents with ceiling enforcement, and can be dynamically adjusted based on operational context.
Data Classification Ceilings
Four tiers — public, internal, confidential, and restricted — with hard ceiling enforcement. An agent at "internal" classification cannot access confidential data, regardless of its trust level. Classification travels with the data, not the request.
Tool Risk Tiers
Three-tier classification: exempt (read-only, always allowed), standard (requires operator trust or above), and elevated (requires conductor trust plus explicit approval). The conductor tier matrix maps trust levels to tool permissions.
Append-Only Audit
SQLite WAL-mode database records every policy decision with full context: agent ID, tool invoked, trust level, data classification, decision outcome, and timestamp. Bounded queue with buffer fallback prevents audit loss under load.
Delegation Mediation
When agents delegate to sub-agents, the governance layer enforces parent ceiling inheritance, breadth limits (max concurrent sub-agents), and depth budgets (max delegation chain length). No sub-agent can exceed its parent's permissions.
Practical Overhead
Policy evaluation adds under 200ms for standard operations. Exempt tools see near-zero overhead. Zero approval prompts for daily development work at trust level 3 and above — governance that protects without interrupting flow.
Why It Matters
Most AI governance is either absent or so restrictive it kills productivity. Teams either run agents with no guardrails and hope for the best, or they lock everything behind approval workflows that make the AI slower than doing the work manually.
BulletproofSoftware.tech's governance layer is designed for the middle ground — where compliance teams need audit trails and developers need to ship code. The trust level system means a developer's daily coding agent operates at trust level 3 with standard tool access and zero approval prompts. But when that agent tries to modify production infrastructure or access restricted data, the policy engine kicks in with appropriate controls.
The TRiSM alignment is not a checkbox exercise. Trust, Risk, and Security Management are embedded in every agent spawn, every tool call, and every delegation. The append-only audit trail means you can prove what happened, when, and why — which is exactly what auditors and regulators ask for.